It's 2025, and malware today is socially engineered. Just installing antivirus software on the PC is not sufficient. Hence, you must take additional steps to ensure complete Windows 10 and Windows 11 hardening. Having security software is only one of the ways, but there are other levels of hardening that you probably don't know.
So, here is a complete Windows 10/11 hardening checklist to protect your PC.
Windows 10/11 Hardening: What should you do?

Are you still using Windows XP, Windows 7, or Windows 8? In that case, upgrading to Windows 10 or the latest version of Windows 11 will be a good idea. I understand that it may appear to be a bit difficult to operate at the beginning. However, once you get used to the interface, it will be a part of your life as any other operating system. So moving forward, this guide will focus on Windows 10/11.
Operating System: Regular Updates
Microsoft officially stopped support for Windows XP on April 8, 2014. Windows 7 met with the same fate on January 14, 2020. Also, support for Windows 8.1 ended on January 10, 2023. Hence, you will not receive any updates from Microsoft on these operating systems. Due to the lack of regular updates and security patches, these operating systems are at higher risk due to recent attacks.
Considering the security point of view, Windows 10/11 should be your choice.
Note: Microsoft has announced the end of support for Windows 10 (Home and Pro) on October 14, 2025.
System Protection: Create a Restore Point
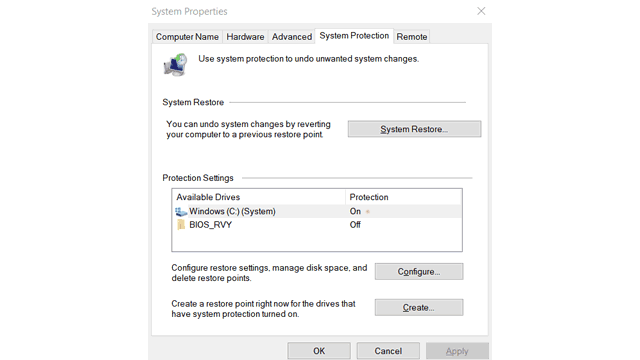
It's always a good practice to have a restore point. When system protection is on, Windows automatically keeps and updates a restore point to which you can revert if you face any issues.
You can also create a manual restore point. Doing so gives you control over the state of Windows where you want to return. I usually create a restore point manually after a fresh installation with a basic set of applications. However, you can also do so as per your choice. A restore point is not helping you directly in Windows 10/11 hardening, but it provides a flag point where you can always return.
Account Settings: Prefer Non-Admin User

By default, we get the access and privileges of administrators on the first account creation of Windows. You should create another user with standard privileges and use it for daily work. It lowers the risk of infection as a standard user account doesn't have all access to the system. For escalated privileges (if necessary), you can use the Admin account.
Encrypt Drives with BitLocker

Drive encryption protects your data from unauthorized access. Since Windows 10/11 includes BitLocker by default, you do not have to spend anything. Also, you can use it to encrypt local and removable storage devices. Learn more about BitLocker and implement the same.
Review Windows 10/11 Privacy Settings

In this section, you can tweak how Windows 10/11 collects your data or apps accesses system resources. In Privacy settings, visit all the sections and disable the options accordingly. I recommend you to disable all the data settings you do not want Microsoft to use. In case you wish to be a part of the Windows Insider Program, you need to enable Full Diagnostics & Feedback.
Monitoring your system's Activity history is crucial for detecting potential compromises. Windows Activity history feature records your device usage, including apps, services, files, and websites you interact with. This information is stored by default, but you can turn off the feature by navigating to Privacy settings > Privacy & security > Activity history.
App permissions are very useful in case you only want to allow certain apps to use your File system. Hence, it will protect you from ransomware attacks. To ensure Windows 10/11 hardening, you should review and limit the apps that can access your Camera and Microphone. There are many more settings that you can tweak in this section.
Note: If you have an antivirus with ransomware protection, you will not have access to change File System as your antivirus actively manages it.
Cleanup: Uninstall Unnecessary Software

The less you have, is better. Avoid the risk by uninstalling software products you don't use. Intruders exploit many popular programs to gain access to your system and infect it. Some prominently exploited software programs are Adobe Flash and Java, so get rid of them unless extremely necessary.
CCleaner, Revo Uninstaller, Avast Cleanup, AVG TuneUp and Uninstaller Pro are reliable solutions to uninstall unnecessary applications and clean up garbage. Also, apps like CCleaner can optimize PC Speed automatically. It is an essential step in Windows 10/11 Hardening. Hence, do not miss it.
Scan Non-Microsoft Products for vulnerability
In Windows 10/11, Microsoft automatically updates the apps that you get from Microsoft Store. Also, you need to update 3rd party software regularly. While updating the software, you also reduce the chances of existing software vulnerabilities. In case you have a lot of applications on your system and find it difficult to update them manually, check the IObit Software Updater. It helps you by automatically updating any software to the latest version.
Windows 10/11 Hardening: Never disable User Account Control
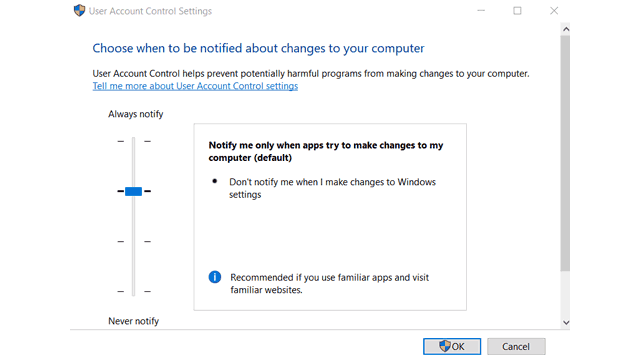
Yes, UAC prompts are annoying, but by disabling them, you lose more than just a pop-up. Disabling UAC also disables file-system & Registry virtualization and Protected Mode. When an application wants to make a system change, like modifications that affect other users, modifications of system files and folders, and installation of new software, a UAC prompt shows up, asking for permission.
User Account Control makes sure that these changes are made only with approval from the administrator. Read more about UAC.
Strong Passwords: Tough to Guess
It is a grave mistake, but it isn't your fault. Hard-to-guess passwords are difficult to remember. Why not use a sophisticated tool to manage and remember all your passwords in a safe Vault? I have been using LastPass for a long time for this purpose. It generates secure passwords as well as stores them in encrypted form. You can get passwords on demand and auto-fill whenever required.
Active Protection: Use Antivirus

It is indeed necessary even after following everything stated above. No matter how many manual actions you take, there should be a program that continuously monitors every activity. It is possible only if you have an Antivirus program.
Windows 10/11 includes Microsoft Defender (formerly known as Windows Defender), and it can protect you from primary threats. Also, the latest additions include ransomware protection by default. However, you should solely depend on it only if you are fully aware of your internet browsing habits. We have covered more in our Internet Safety Facts article that also includes tips to stay safe online.
Note: Enable "Controlled folder access" in Defender settings. It is OFF by default, and it is the Ransomware protection.
I recommend more than just a plain antivirus like an Internet Security program that has an inbuilt firewall and spam protection. Bitdefender Total Security is a perfect choice with advanced antivirus protection, two-way Firewall protection, and Cloud-Antispam. Read out full Bitdefender Total Security review for more details.
We have reviewed some of the top antivirus programs so you can find the best antivirus as per your requirement.
Update Windows Device Drivers
Updating device drivers is essential. Not only it keeps your devices at optimal performance level, but also prevents any exploits that may exist in older versions. Windows 10/11 automatically updates the device drivers for you. However, if you feel that you are not receiving proper driver updates, you can check a 3rd party driver updater like Driver Booster Pro.
Windows Sandbox
It is a secure virtual environment on your computer. It allows you to run a fresh installation of Windows, which is completely separated and isolated from your current installation (host machine). It is most beneficial for trying out suspicious programs without risking your system's safety.
Unfortunately, the Sandbox feature is exclusive to Windows Pro and Enterprise suites. However, you can install third-party alternatives like VirtualBox and Sandboxie Plus to enjoy the same benefit of a virtual environment similar to Windows Sandbox.
To activate Windows Sandbox, follow these steps:
- Open Control Panel.
- Click on "Programs and Features."
- Select "Turn Windows features on or off."
- Check the box next to "Windows Sandbox."
- Hit "OK"
Note: You should enable Windows virtualization to use the Windows Sandbox feature.
Core isolation
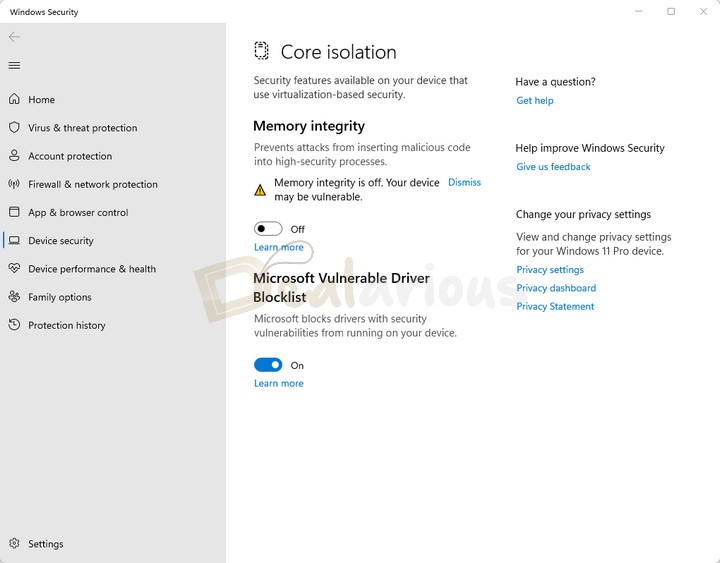
Turning on the Core isolation feature makes your Windows system more secure by protecting important core processes by running them in a virtualized environment during malicious attacks. You can find this feature under Device security.
Memory integrity is an essential element of the Core isolation feature. It separates high-security processes from the rest, preventing malicious codes from accessing them during an attack.
Find my device

Find my device is a feature in Windows 10 and Windows 11 that helps you locate your lost or stolen Windows device. To use it, you must have a Microsoft account and be an administrator.
Note: Make sure you turn on the Location settings before using it.
To turn On "Find my device," go to Settings and then choose either "Privacy & Security" in Windows 11 or "Update & Security" in Windows 10.
App and Browser Protection
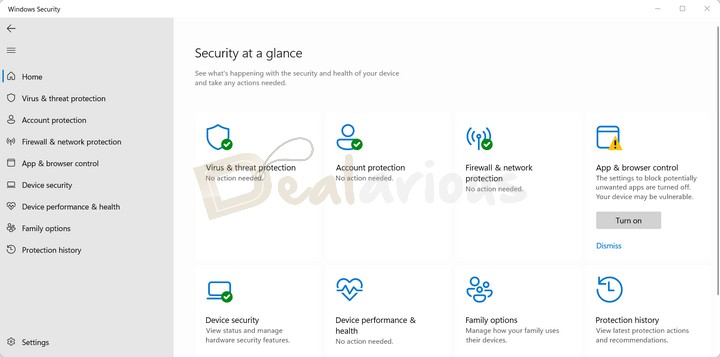
App & browser control is a part of Windows Security. It is designed to prevent and manage tools to safeguard your Windows system from snoopy malicious apps and websites.
The feature utilizes Reputation-based protection and Exploit protection in safeguarding your device. Reputation-based protection is Off by default in Windows. Hence, enabling the feature is recommended to enjoy a safer Windows environment. You can do so by going to Windows Security > App & browser control > Reputation-based protection.
Note: However, it's worth noting that the "Force randomization for images (Mandatory ASLR)" in Exploit protection is turned Off by default. It is recommended to only enable it if necessary for specific reasons.
Application Guard
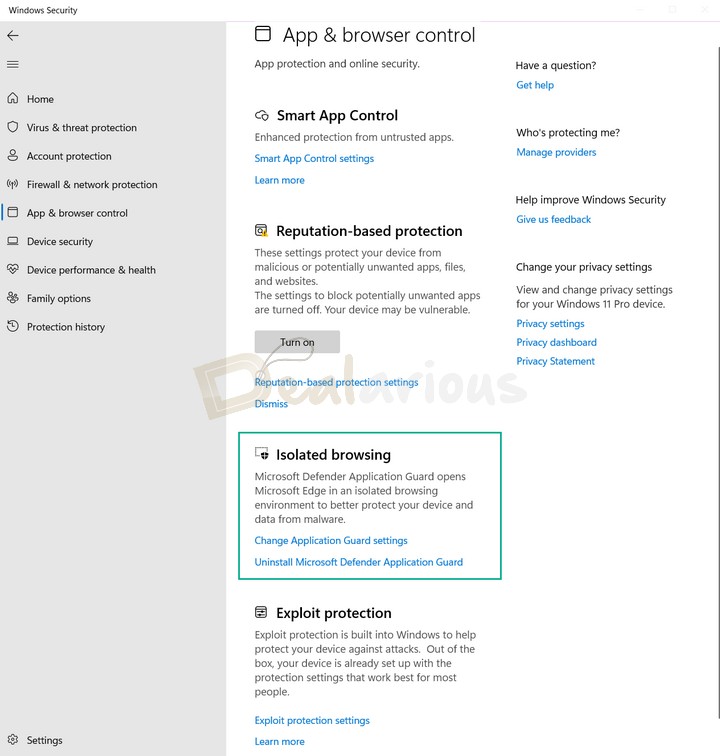
Like Windows Sandbox, Application Guard allows you to create an isolated browsing environment using Microsoft Edge. This feature is useful when visiting a suspicious website, as it ensures that potential threats won't harm your main system.
Moreover, if you prefer using Chrome or Firefox as your default browser, you can benefit from Application Guard by installing its extension for these platforms.
Note: Application Guard is only available for Windows Pro and Windows Enterprise. Also, to use this feature, your device must have virtualization support and should be enabled in the BIOS settings.
To activate the feature, follow these steps:
- Open Control Panel.
- Click on "Programs and Features."
- Select "Turn Windows features on or off."
- Check the box next to "Microsoft Defender Application Guard."
- Click "OK" to install Application Guard and its necessary components.
Frequently Asked Questions(FAQs)
Do I still need an Anti-Malware?
If you have followed everything till now, you probably won't need one. Also, if you are using a primary antivirus, it is not recommended to use another real-time protection. However, if you want to have an additional layer of security, you can use an anti-malware with real-time protection off. Hence, you have to perform another scan manually. The good idea is to perform a full system scan weekly manually. If you wish, you can give Malwarebytes a try.
How do I protect myself from risky Websites?

If you use Bitdefender Total Security, it comes with a real-time URL checker which notifies you about malicious websites. You can avoid visiting them or go ahead by adding them as an exception. In any case, you will not accidentally land on malicious websites. Apps like Advanced SystemCare Pro also implement features like Host file and browser Homepage protection. You can learn more about the functionality in this Advanced SystemCare Pro Review.
Does Windows 10/11 Hardening protect my Online Privacy?
Unfortunately, the answer is NO. The tweaks in this guide only allow you to protect the Windows 10/11 environment. However, if your concern is with online privacy, then you should use a VPN. With the increase of ISP monitoring, a VPN is a must-use service. A misconception among many people is that a VPN is only needed to access geo-restricted content. Well, it is not precisely correct.
Apart from letting you access streaming content and services, a VPN also encrypts all your connections using various Tunneling protocols. Also, many new VPN services like Surfshark provide advanced features like ads, Malware, and tracker blocker. Hence, you should use a VPN regularly, especially when using public Wi-Fi.
Conclusion
So this concludes the Windows 10/11 Hardening checklist. This article includes all the tricks that will make your Windows 10 and Windows 11 safer. However, always remember that you have to be careful with every Windows update and check for the changes in the new version. If there is any change in the privacy sections, you will have to change the particulars accordingly.
Comment below and let me know if you have any more questions.
Sourojit is Executive Editor at Dealarious. Rumor says He is Computer Science Engineer; He neither accepts it nor denies it. Tech Explorer, Philosopher and a Storyteller.
Excellent checklist to make sure the windows is secure from viruses and malwares. Between i prefer windows 7 to do better tweaks and take control of the security area of the PC. Windows 8 has all the features but they are not easily accessible and less ways to tweak them.
Good article you have here to protect our data from internet attacks (Y). Cheers.
Robin.
Hi Rohit,
Many believe that after installing antivirus, the computer is totally secured, Hell No! there are still some security measure to apply to secure the computer, installing antivirus is just among the list
if u have some virus/mailware, and doesnt noticed this, what problem u have at this time really ?
i have no UAC
i haver bitdefender total sec,
i have the UP- DOWN load rate show at task. to see it nonstop, because i can down with 200Mbit and up with 12mbit…
soooo, if i have any virus/mailware onboard, and ingame my ping doesnt goes over 20, dont notice some CPU RAM or NET load, there i dont have make at myselfe, wtf does some “viruses/mailware” ? i doesnt scarred, and all people get spend monney 4 this scarry thing who are at the end doesnt make u pain, u dont noticed u only scarred 4 this ? if i get paranoid, i can shut down the pc, and choose some backup thats me doesnt let get paranoid freaky.
sometimes i think, all people are think ” OMMMMGGG have MAILWARE, one day longer, and the police comes, brake my dore and fuc*s me in the ass 24/7 365 ,….
are u scarry ?